IT外包桌面解決方案--SQL注入漏洞過程實例及解決方案
2020-03-30 16:21 作者:艾銻無限 瀏覽量:
與眾不同的服務是因為有心

所有艾銻人可能都知道艾銻無限為客戶提供三種與客戶接觸的方式,一種是產品,一種是技術,還有一種是服務,那這三種所謂的方式構建起一個三角形,這種穩固的體系,看起來還不錯,但我們細細思考卻發現很多企業也都提供這三種方式與客戶建立一個長久的關系。
那艾銻無限到底與這些企業有什么區別呢?有什么明顯的區別,讓客戶和其他人一看這種服務就明白是艾銻無限的服務,這個世界上獨一無二的服務呢,大家都看過3D電影吧,無論后來的技術提升或其他人如何模仿,如何超越,大家首先可能想到的3D電影的代表作是《阿凡達》,是的這就是獨一無二,那如何讓我們的三種與客戶建立聯系的方式也能變的立體呢,我們來看怎樣把這三種方式賦予生命,讓他們與眾不同.
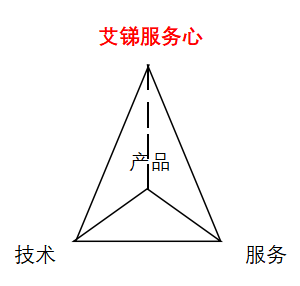
大家可能已發現原來“艾銻服務心”讓我們的服務變的立體,開始有了美感,開始賦予了新的生命,而不是之前人們認為的那種“無聊”,沒有生趣的服務,這是一種全新的與客戶建立聯系的方式,與客戶產生互動的方式,這是生命與生命的互動,這是靈魂與靈魂間的碰撞,就像我們的每一顆蒲公英種子一樣讓每一次與人的接觸都賦予了生命,而不是人與機器的單調互動,更不是那種看起來死氣沉沉的三角形。我們用我們的愛,付出,喜悅轉化出我們的誠心,細心,貼心的彼此體驗,讓更多的三面體不斷去聚合,形成一顆璀璨的鉆石。
SQL注入漏洞過程實例及解決方案
代碼示例:|
1
2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
public class JDBCDemo3 {public static void demo3_1(){boolean flag=login("aaa' OR ' ","1651561"); //若已知用戶名,用這種方式便可不用知道密碼就可登陸成功if (flag){System.out.println("登陸成功");}else{System.out.println("登陸失敗");}}public static boolean login(String username,String password){Connection conn=null;Statement stat=null;ResultSet rs=null;boolean flag=false;try {conn=JDBCUtils.getConnection();String sql="SELECT * FROM user WHERE username='"+username+"'AND password='"+password+"'"; //此處是SQL注入漏洞的關鍵,因為是字符串的拼接,會使查詢語句變為:SELECT * FROM user WHERE username='aaa' OR '' AND password='1651561',此查詢語句是可得到結果集的,便出現此漏洞stat=conn.createStatement();rs=stat.executeQuery(sql);if(rs.next()){flag=true;}else{flag=false;}} catch (SQLException e) {e.printStackTrace();}return flag;} |
|
1
2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 |
public static void demo3_1(){boolean flag=login1("aaa' OR ' ","1651561");if (flag){System.out.println("登陸成功");}else{System.out.println("登陸失敗");}}public static boolean login1(String username,String password){Connection conn=null;PreparedStatement pstat=null;ResultSet rs=null;boolean flag=false;try {conn=JDBCUtils.getConnection();String sql="SELECT * FROM user WHERE username=? AND password=?"; //使用?代替參數,預先設置好sql格式,就算在輸入sql關鍵字也不會被sql識別pstat=conn.prepareStatement(sql);pstat.setString(1,username); //設置問號的值pstat.setString(2,password);rs=pstat.executeQuery();if(rs.next()){flag=true;}else{flag=false;}} catch (SQLException e) {e.printStackTrace();}return flag;}} |
相關文章
 關閉
關閉